IoT Security Services
Boost your investor confidence and keep the trustworthiness of your business high by using IoT security consulting from experts with 15+ years on the market.
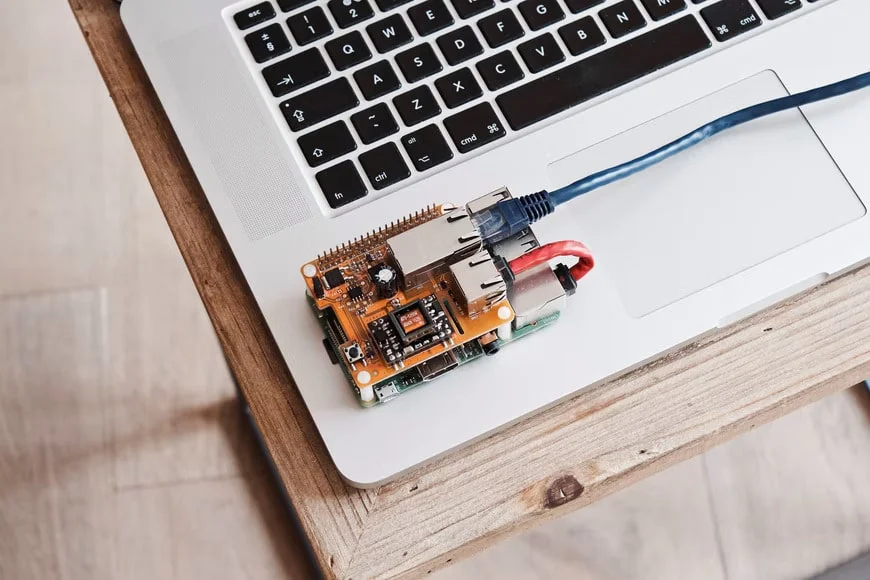
IoT cybersecurity services by Yalantis
Benefits of IoT security solutions by Yalantis
Extensive IoT Security solutions
Our experience with delivering secure development lifecycles, vulnerability management, and IoT devices hardware security makes us a reliable IoT security consultant.
Compliance and Consulting Expertise
As an ISO-certified company, we at Yalantis ensure adherence to industry-specific regulations such as SOC2, FedRAMP, and PCI DSS.
Industry-Specific IoT Expertise
Yalantis uses its proven expertise in healthcare, manufacturing, automotive, agriculture, and many other domains to provide trustworthy IoT Security.
Proactive Threat Mitigation
Yalantis emphasizes proactive measures to safeguard IoT devices and data from potential cyber threats via secure code development, threat modeling and risk assessment.
Success stories to show our expertise
Industry-specific IoT services

Healthcare IoT
Enhance patient care and operational efficiency through connected medical devices, remote patient monitoring, and predictive analytics.


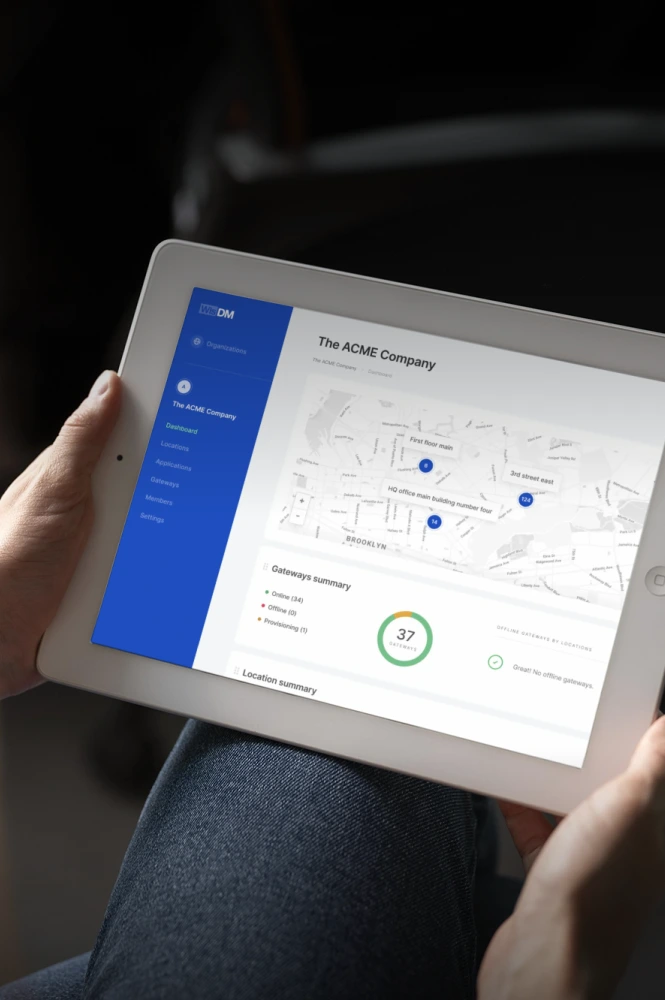
Industrial & Manufacturing IoT
Optimize production, ensure equipment uptime without breakdowns, and improve safety with IoT-powered asset monitoring and predictive maintenance.

Logistics & Supply Chain IoT
Enable real-time tracking, inventory optimization, and seamless logistics with connected systems for greater transparency and efficiency.

Automotive
Improve driving experiences and safety with connected vehicle systems, predictive maintenance, and autonomous technologies.


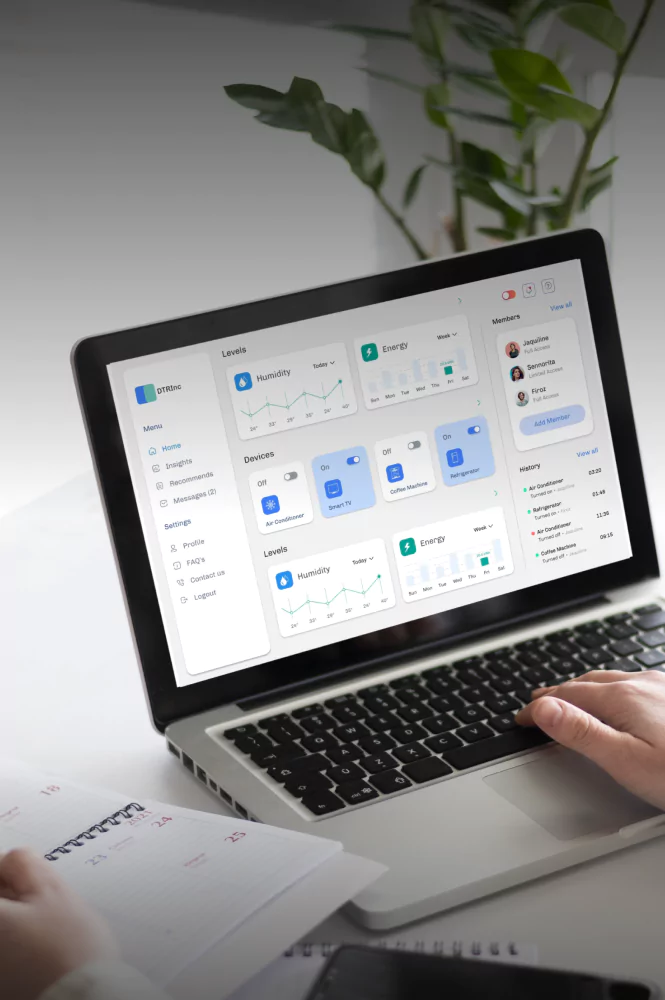
Smart Building
Streamline smart living and steady operations via connected devices, energy management, and automated controls.


Agriculture
Transit to sustainable practices with IoT-based precision farming, livestock monitoring, and real-time environmental analytics.

Testimonials from our clients
IoT Consulting and development insights
The Role of Edge Computing in IoT and Business Growth
Get a complete understanding of how edge computing works in IoT, its benefits, and IoT challenges it helps to solve. Find out when exactly you can use edge computing in IoT.

The Ultimate Guide to IoT Testing: Catch Failures Before Your Customers Do
Master the complexities of IoT quality assurance with our comprehensive guide. Learn how to validate device-to-cloud synchronization and ensure ironclad security across your entire IoT network.
How can IoT suppliers build industrial IoT software to attract new customers?
Learn the specifics of industrial IoT development to cover IoT vendors’ and their customers’ needs related to large-scale industrial IoT monitoring.
FAQ
What do your IoT security services include?
Our IoT security services cover device authentication, data encryption, secure firmware updates, cloud access control, and threat detection. We provide end-to-end protection across your IoT ecosystem to be sure that each layer, from hardware to cloud, is secured against current vulnerabilities and cyberattack vectors.
How does your IoT consulting reduce security risks?
Where necessary, we incorporate IoT security consulting into every project stage. Typically, we start with risk assessments and architecture reviews. We help partners identify vulnerabilities early, embrace secure development practices, and guarantee compliance. This approach significantly reduces exposure to threats across your connected systems.
How do IoT security solutions protect data and privacy?
Yalantis’ IoT security solutions operate with encryption protocols, role-based access control, and secure communication channels to protect sensitive data. Combined with secure firmware and cloud-side protections, these measures ensure that both device-level and user data privacy are always maintained.
How do you ensure secure onboarding of IoT devices?
To successfully onboard all the required sets of devices, we utilize certificate-based authentication, zero-touch provisioning, and secure boot processes. These methods, combined with our IoT cybersecurity services, ensure each device is verified, trusted, and shielded from unauthorized access right from deployment.
Do you consult on IoT security in regulated industries?
Yes, our IoT security consulting services support regulated sectors like healthcare, automotive, finance, and other strictly regulated sectors. We guide you through compliance with industry-specific standards such as HIPAA, GDPR, and ISO 27001, providing secure, audit-ready implementations for critical applications.
What compliance standards do your solutions support?
Our IoT cybersecurity solutions align with leading standards such as ISO 27001, NIST, GDPR, HIPAA, and ETSI EN 303 645. We help you execute security controls and documentation that meet compliance requirements and improve resilience against evolving threats.
What industries benefit most from IoT security implementation services?
Some of the industries that benefit the most from implementing IoT security services are healthcare, industrial automation, smart homes, and transportation. These sectors run sensitive data and depend on reliable device performance, so security is essential for operational safety and regulatory compliance.
Do you provide monitoring and threat detection for IoT?
Yes. As part of our IoT cybersecurity services, we offer continuous monitoring, anomaly detection, and automated alerts. These services help detect and respond to suspicious activity quickly, which is crucial for minimizing downtime and improving the overall resilience of your IoT infrastructure.
How do your services scale with connected device fleets?
Our IoT security testing and architecture reviews guarantee your security measures can scale alongside your device fleet. We implement centralized access control, automated updates, and monitoring tools that protect thousands of devices across locations and networks.
Why choose Yalantis as your IoT security partner?
Yalantis combines deep tech expertise with proven IoT cybersecurity solutions, offering full-cycle support, from architecture and compliance to real-time threat detection. We design and implement security strategies, adapted to your needs, ensuring safe, scalable, and regulation-ready IoT deployments that support business growth.
Contact us

got it!
Keep an eye on your inbox. We’ll be in touch shortly
Meanwhile, you can explore our hottest case studies and read
client feedback on Clutch.

Nick Orlov
IoT advisor
Your steps with Yalantis
-
We get on a call
-
We discuss your project
-
We prepare and offer you our solution
-
We start our way to achieving our goals!