Yalantis provides specialized industrial IT services for legacy machinery modernization, building secure hardware gateways and Rust-based middleware that connect 20-year-old PLCs to the cloud.
Legacy Modernization Services for Manufacturing Industry
Empowering to drive success






Keep an eye on your inbox. We’ll be in touch shortly.
Meanwhile, you can explore our hottest case studies and read client feedback on Clutch.
Challenges Legacy System Modernization Solves
The “Protocol Zoo” blocking OT/IT convergence.
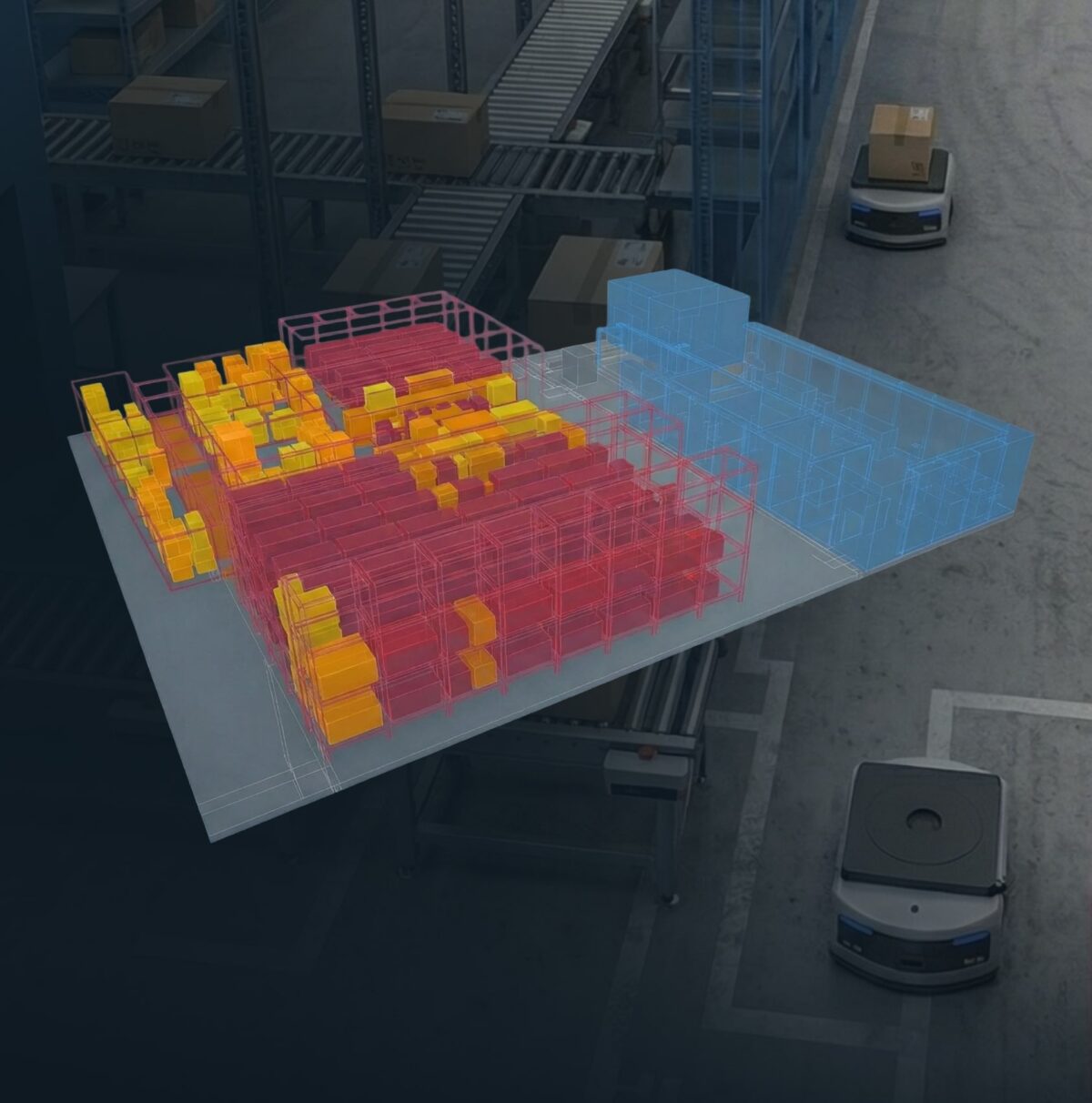
Manufacturing floors often rely on a mix of 50+ diverse protocols (like Modbus and Profibus) that don’t communicate with modern infrastructure, trapping valuable data in isolated silos. This fragmentation hinders the unified view necessary for advanced analytics. Legacy modernization services provide the translation layer to normalize this “protocol zoo” into cloud-ready standards like MQTT and OPC UA.
Hardware dependency risks from obsolete industrial PCs.
Critical production systems running on discontinued Windows XP/7 hardware face imminent failure risks, where a single motherboard issue can halt an entire line. Spare parts are unavailable, and stabilization is urgent. Legacy application modernization through Physical-to-Virtual (P2V) migration eliminates these hardware dependencies, preserving the original, trusted HMI logic while removing the threat of unrepairable physical failure.
Undocumented legacy code creating operational blind spots.
Decades-old PLC programs often lack documentation, leaving teams reliant on lost “tribal knowledge” where even minor modifications risk operations. This lack of visibility keeps teams dependent on black-box systems. Legacy code modernization through reverse-engineering recovers this institutional knowledge, creating maintainable, documented systems that reduce operational risk and extend the life of critical production assets.
“Dumb” assets invisible to enterprise systems.
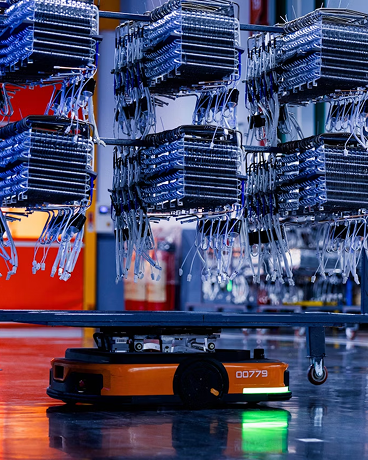
Functional but unconnected machinery generates zero data for MES or predictive maintenance, yet replacing reliable equipment offers poor ROI. Brownfield connectivity solutions extract data from these assets using minimally invasive techniques that do not disrupt certified control loops or void warranties. This approach bridges the gap to smart manufacturing, unlocking real-time process optimization without the capital expenditure of new machinery.
Air gap security requirements blocking cloud integration.
While “air gaps” isolate OT networks for safety, they prevent the data flow required for industrial digitalization. Generic IT bridges used to cross this gap often introduce unacceptable vulnerabilities, especially as cyberattacks on manufacturing rise. Secure OT/IT bridge implementation provides compliant data pipelines that respect the air gap, enabling cloud integration while strictly adhering to IEC 62443 standards and EU Cyber Resilience Act requirements.
Outdated HMI interfaces increasing operator error.
Button-heavy, character-based interfaces from the 1990s slow workflows and increase training time. These obsolete systems also prevent remote visibility into operations. HMI modernization replaces these interfaces with intuitive, web-based touchscreens that reduce human error and streamline user experience, allowing employees to focus on higher-value work rather than fighting with antiquated technology.
Yalantis Legacy System Modernization Services
Discuss Your Legacy Infrastructure with our architect.
We offer a free consultation to define your goals, understand your current factory floor situation and create an action plan on improving your manufacturing operations.
Legacy Modernization Solutions for Different Industries
While our main expertise lies within Healthcare, Logistics & Supply Chain, Automotive and Industrial Manufacturing, we have proven experience and are open to delivering tech solutions in other industries.
Benefits of Developing a Legacy Modernization Solution with Yalantis
Eliminate Hardware Dependency Risks
Our P2V migration expertise transforms vulnerable physical infrastructure into resilient virtual environments. By eliminating hardware dependency, you reduce vulnerability to failures and cyber threats, addressing the increased risks legacy equipment faces from modern attack surfaces. This approach helps manufacturers reduce downtime from discontinued components and single points of failure that can halt production operations without warning.
Preserve Capital Investment in Functional Assets
Our brownfield connectivity approach extracts more value from existing machinery without expensive “rip and replace” projects. By enabling real-time information collection and integration, these solutions help optimize the use of existing infrastructure, leading to production efficiency and reduced waste. Get modern connectivity and analytics capabilities while protecting your capital expenditure and supporting business growth.
Unlock Trapped Operational Intelligence
Our protocol normalization expertise unifies information from the “protocol zoo” into cloud-ready formats, enabling predictive maintenance, machine learning analytics, and enterprise visibility that was previously impossible. By creating a unified information architecture, we ensure comprehensive insights are readily accessible, empowering informed decisions and supporting advanced smart manufacturing initiatives across your manufacturing operations.
Ensure Regulatory Compliance & Security
Our compliance-first approach bakes IEC 62443 security standards into the development process. We take a proactive, strategic approach to cybersecurity, integrating it into architecture design and risk mitigation to ensure regulatory compliance with standards such as NIST and CMMC. Rust-based firmware prevents memory vulnerabilities that plague legacy C++ stacks, meeting EU Cyber Resilience Act requirements and addressing the unique challenges of industrial modernization.
Reduce Operator Error & Training Time
Our HMI modernization expertise creates intuitive interfaces that reduce cognitive load and accelerate onboarding. By minimizing human error and supporting employees in their day to day operations, these solutions help new employees become productive faster, while experienced operators make fewer mistakes—directly contributing to cost savings across your organization.
Hardware + Software DNA
We don’t just write code—we design the PCBs, enclosures, and edge gateways in our in-house R&D lab. This full-stack capability means we build the physical bridge (custom hardware) and the digital bridge (middleware) that legacy vendors don’t offer, providing legacy manufacturing solutions that address manufacturing system modernization gaps.
What our clients say
Legacy Modernization Insights
How IoT is transforming the manufacturing industry
Discover how IoT in manufacturing makes processes more efficient and cost-effective through predictive maintenance, quality control, and inventory management.

How Medical Device Manufacturers Can Shift From Hardware-Only Model to Cloud Software to Reduce Costs and Enable Recurring Revenue
Discover how medical device manufacturers are shifting to cloud-based software to reduce costs, improve patient outcomes, and unlock recurring revenue streams.

How Manufacturers Use IoT for Predictive Maintenance
Learn about the benefits of Internet of Things predictive maintenance for large manufacturers and how a web application can increase its effectiveness.
FAQ
-
How do you extract information from legacy PLCs without voiding warranties or disrupting certified control loops?
Our approach is fundamentally non-invasive. We design custom “sidecar” edge gateways that tap into legacy communication ports (RS-232, RS-485, Modbus RTU) as passive listeners—the gateway reads information without injecting commands into the control network. This ensures the core safety logic of your equipment remains completely untouched. For assets without accessible ports, we deploy external sensors (vibration, temperature, current clamps) that monitor machine behavior without any physical connection to the control architecture. This approach has been validated with equipment from major OEMs including Siemens, Fanuc, and Omron, ensuring warranty compliance while enabling full connectivity. The key takeaways here are that you can achieve complete visibility into your manufacturing environments without risking production stability or voiding equipment warranties—a critical consideration for organizations where unplanned stoppages directly impact revenue and customer commitments.
-
What is the process for implementing legacy modernization with your team?
The process follows a structured six-phase methodology designed to support your digital transformation efforts: First, we conduct a comprehensive legacy asset inventory and dependency mapping, documenting every piece of equipment, its condition, and its integration points. Second, we define the transformation strategy—determining whether each component should be replaced, refactored, wrapped, or virtualized based on business criticality and technical feasibility. Third, we plan information migration, including schema mapping and historical record preservation requirements. Fourth, we design and develop the new architecture with parallel testing against production behavior. Fifth, we plan the cutover, train operators, and document fallback procedures. Finally, we execute production cutover with hypercare support and post-migration optimization to ensure peak performance. This methodology ensures decision makers have clear visibility at every stage, with defined milestones and measurable outcomes that validate progress toward your it modernization goals. Throughout the engagement, we maintain transparent communication so your leadership team understands exactly where the project stands and what value has been delivered.
-
How do you handle security when bridging OT networks to cloud infrastructure?
Security is foundational to our approach, not an afterthought. We implement secure OT/IT bridges that respect the intentional “air gap” in your industrial networks. Our edge gateways use Rust-based firmware specifically to prevent the memory safety vulnerabilities (buffer overflows, use-after-free) that are common attack vectors in legacy C/C++ embedded software. Information flows through encrypted channels with certificate-based authentication to cloud platforms. We architect solutions to be compliant with IEC 62443 (Security for Industrial Automation) from the start, and our approach meets EU Cyber Resilience Act requirements. Network segmentation ensures that even if cloud connectivity is compromised, attackers cannot reach your control equipment. This security-first methodology is essential for organizations in the manufacturing sector where production continuity and intellectual property protection are paramount—a breach could expose proprietary processes or enable competitors to reverse-engineer your operational advantages.
-
Can you virtualize legacy environments running Windows XP or older operating platforms?
Yes, our P2V (Physical-to-Virtual) migration service specializes in exactly this challenge. We capture complete images of legacy industrial PCs—including the OS, device drivers, HMI software, communication configurations, and licensing—and convert them to virtual machines that run on modern hypervisors (VMware ESXi, Microsoft Hyper-V). The virtualized environment behaves identically to the original physical machine, preserving timing-sensitive operations and protocol communications. Hardware abstraction means you’re no longer dependent on discontinued motherboards, proprietary I/O cards, or aging storage. We’ve successfully virtualized environments running Windows XP, Windows 7 Embedded, and even older Windows NT installations. This manufacturing it modernization approach ensures your daily routine continue uninterrupted while eliminating the risks associated with obsolete hardware that could cause supply chain disruptions if critical equipment fails unexpectedly. The virtualized approach also simplifies disaster recovery—virtual machine snapshots can be restored in minutes rather than the days required to rebuild physical hardware.
-
How long does legacy modernization typically take, and what ROI can we expect?
Timeline varies based on scope: a single-machine HMI modernization may take 6-8 weeks, while enterprise-wide P2V migration across multiple facilities typically spans 6-12 months with phased rollouts. We recommend starting with a strategic pilot on high-risk assets to demonstrate value quickly. ROI comes from multiple sources: elimination of emergency downtime from hardware failures (which can cost $10,000-$50,000+ per hour in manufacturing), reduced maintenance costs through condition monitoring, extended asset lifespan avoiding capital replacement costs, and productivity gains from modern operator interfaces. Clients typically see payback within 12-18 months, with ongoing savings compounding as more assets are modernized. Beyond direct savings, industrial process modernization enables new revenue streams—OEMs can offer connected services to customers, and manufacturers gain the operational intelligence needed to optimize supply chains and improve customer loyalty through more reliable delivery performance. The competitive advantage compounds over time as connected assets generate insights that drive continuous improvement across your entire operation.
-
How does your solution integrate with existing CMMS, MES, and ERP platforms?
Seamless integration is essential to operationalizing the intelligence we extract from legacy assets. Our middleware layer exposes standardized APIs (REST, OPC UA) that allow your existing enterprise platforms to consume real-time operational information. For CMMS integration (SAP PM, Maximo, Fiix), we can automatically generate work orders when condition monitoring detects anomalies. For MES platforms, we provide the real-time production information that enables accurate OEE calculations and genealogy tracking. For ERP solutions, we bridge the gap between shop floor reality and enterprise planning, providing visibility into inventory levels and supply chain management processes. The key is that we adapt to your existing IT landscape rather than requiring wholesale replacement—our solutions are designed to complement and enhance your current technology investments. This approach leverages ai tools and advanced analytics capabilities within your existing infrastructure to transform raw sensor readings into actionable insights that improve manufacturing processes. Whether you’re running SAP, Oracle, or industry-specific platforms, we build the connectors that make modernization additive rather than disruptive.
-
What makes Yalantis different from other legacy modernization vendors?
Three key differentiators set us apart. First, we have Hardware + Software DNA. We don’t just write code; we design custom PCBs, edge gateways, and industrial enclosures in our in-house R&D lab. This full-stack capability means we can build the physical bridge that software-only vendors cannot provide, keeping pace with technological advancements while addressing the practical realities of brownfield environments. Second, our Compliance-First Engineering approach bakes IEC 62443 and ISO 27001 security standards into the development process from day one, not as a post-hoc certification exercise. Third, we specialize in the “Hidden Champion” market — mid-market manufacturers and OEMs with specialized requirements that don’t fit the one-size-fits-all solutions from large industrial automation vendors. We understand that your brownfield environment is unique, and we engineer solutions specifically for your operational context. Our deep focus on industrial clients means we understand the real-world constraints of production environments where uptime is non-negotiable and technological changes must be implemented without disrupting operations or compromising safety certifications.
Let’s Start from call scheduling
- Schedule a call
- We collect your requirements
- We offer a solution
- We succeed together!
Thank you for contacting us.
Keep an eye on your inbox. We’ll be in touch shortly
Meanwhile, you can explore our hottest case studies and read
client feedback on Clutch.